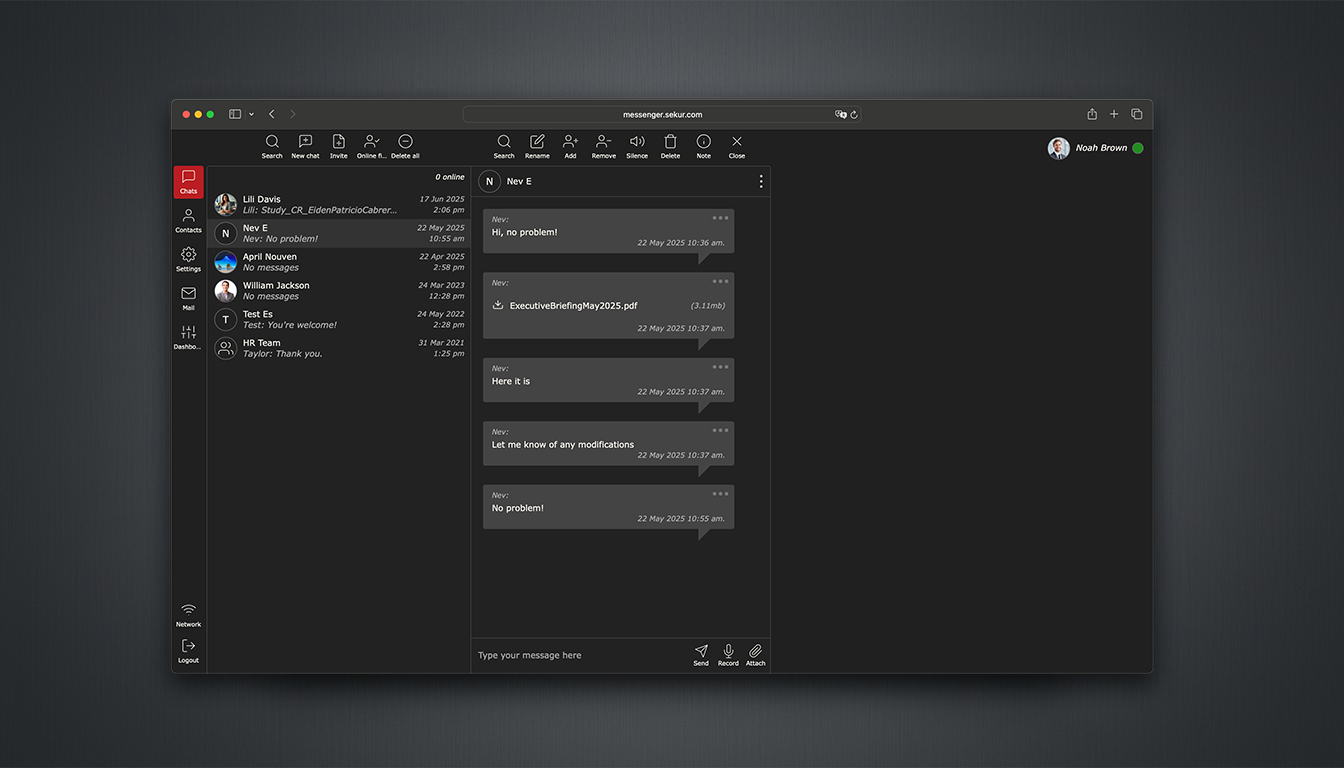
A hardened, invite-only messaging platform engineered for controlled communications. SekurMessenger eliminates reliance on phone numbers, telecom identity, and public infrastructure, supporting the secure handling of sensitive data, including Controlled Unclassified Information (CUI), within a contained environment.
Channel Secured
Invite-only access active
Controlled Communications Environments
Government & Defense Coordination
Mission-critical communications executed without reliance on public messaging infrastructure or exposed identity layers. Controlled access, isolated routing, and clear jurisdiction reduce external visibility and operational risk.
Executive Coordination
Board-level and C-suite communications conducted without exposure to contact syncing, identity mapping, or external messaging networks. Strategic decisions remain contained within a controlled environment.
Legal and Advisory Communications
Privileged discussions maintained within a closed communication loop, reducing exposure from metadata trails and third-party platforms. Controlled access and defined retention support institutional confidentiality.
Financial Operations
Deal teams, investor relations, and due diligence executed without reliance on public messaging infrastructure. Time-sensitive coordination with controlled access and lifecycle management.
Non-Permissive Messaging Protocols
Restricted Node Access (Invite-Only)
Access is strictly limited to vetted participants. No public discovery, no directory indexing, and no external signal penetration.
Zero Retention Comms Protocol
Messages are not retained beyond their defined lifecycle. Once expired, they are removed across all devices with no recovery.
Structural Domain Control
Centralized administrative authority over group integrity. Structural prevention of message forwarding, duplication, or unauthorized egress.
Non-Attributed Identity
Identity is established via secure email protocols. Complete decoupling from telecommunications infrastructure prevents social engineering and SS7-level exploits.
Signature Suppression (Zero Metadata)
Zero access to contact lists, location services, or device telemetry. Your communication patterns remain invisible to third-party observers.
Quantum-Resistant Architecture
Multi-layer 2048-bit encryption utilizing the HeliX protocol. Engineered for post-quantum resistance within a contained Swiss environment.
Prevention of Unsolicited Communication
By removing open-network exposure, communication is limited to trusted participants, reducing the risk of impersonation, unauthorized outreach, and data leakage.
-
Access Control Communication occurs only between approved participants. No phone numbers. No external discovery.
-
Operational Control User access and roles are centrally managed with enforced communication boundaries.
-
Message Lifecycle Messages exist only within defined retention parameters and can be removed across all devices.
-
Audit Visibility All communication activity is recorded for audit purposes. Message content remains inaccessible outside authorized controls.
SekurMessenger: Contained Messaging
Commission deployments based on operational scale and communication lifecycle requirements.
Private
Invite-only communication access
No phone number dependency
No unsolicited contact
- End to end encrypted text and voice messages
- Private group chats
- File transfer size 5GB
- Encrypted chats with non-app users
- No phone number needed
- Sekur ID for full Privacy
- Private Contacts
- Deletion messages on recipient's device
- 2 factor authentification
- Self-Destruct Timer for all messages
- Unlimited Web and App access
Operational
Team messaging under controlled access
Managed participant approval
Configurable message lifecycle
- End to end encrypted text and voice messages
- Private group chats
- File transfer size 5GB
- Encrypted chats with non-app users
- No phone number needed
- Sekur ID for full Privacy
- Private Contacts
- Deletion messages on recipient's device
- 2 factor authentification
- Self-Destruct Timer for all messages
- Unlimited Web and App access
- Admin Onboarding
- Message Archiving
Command
Organization-wide messaging governance
Centralized control across all users
Retention and audit alignment
- End to end encrypted text and voice messages
- Private group chats
- File transfer size 5GB
- Encrypted chats with non-app users
- No phone number needed
- Sekur ID for full Privacy
- Private Contacts
- Deletion messages on recipient's device
- 2 factor authentification
- Self-Destruct Timer for all messages
- Unlimited Web and App access
- Admin Onboarding
- Message Archiving
- Company Directory
- Password policies
- Communications control/restrict outbound
High-Volume Deployment & Custom Architecture
For organizations requiring multi-departmental integration, air-gapped configurations, or GSA-schedule procurement. Tailored security posture for defense, government, and regulated industries.
Initiate Strategic ConsultationStrategic Volume Licensing: Tiered pricing for 500+ seat deployments
White-Glove Migration Concierge: Full-spectrum transition from legacy messaging platforms
On-Premise Integration: Air-gapped deployment within defined perimeters
Dedicated Liaison: Direct access to Sekur technical leadership
The Sovereign Communication Stack
Achieve 100% decoupling from the public grid across all vectors. Structural redundancy ensures your entire signal perimeter is hardened.
Premium Corporate
Core Components
Mail, Messenger, VPN
Infrastructure
500 GB Storage / Password Policy
Support
Migration Concierge
Corporate Plus
Core Components
Mail, Messenger, VPN + Voice/Video
Infrastructure
500 GB / Advanced Admin Controls
Support
Priority Onboarding
On-Premise Deployment
Deploy within your own infrastructure with full administrative control. No external cloud, no third-party routing. Communication remains contained within your operational environment.
Explore deployment optionsEstablish Procurement Channel
Initiate architectural review, obtain deployment specifications, and establish institutional procurement protocols.