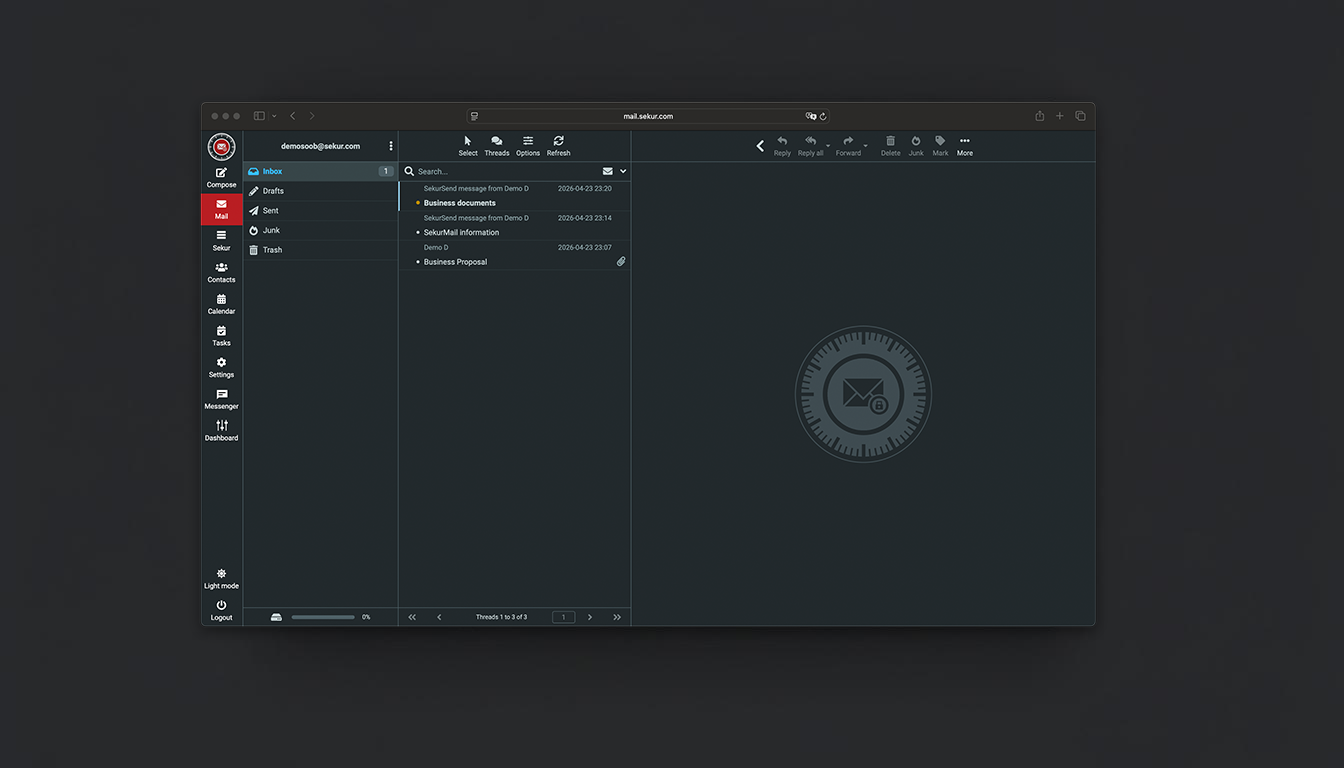
A proprietary email environment designed to keep sensitive communications within a controlled perimeter. No external SMTP routing. No third-party cloud exposure. Communications remain contained under defined operational control.
HeliX Encryption Active
2048-bit multi-layer protection
Where SekurMail Operates
National Security & Diplomacy
Inter-agency coordination and diplomatic signal protection. Leveraging Swiss jurisdictional neutrality to shield sensitive communications.
Executive Control
Board-level strategy, M&A intelligence, and sensitive leadership transitions. Information remains structurally isolated from external observation.
Privileged Legal Operations
Secure attorney-client correspondence with zero metadata footprint. Ensures absolute compliance with evidentiary and privilege standards.
Regulated Operations
High-value deal flow, investor relations, and regulatory reporting. Data is maintained within a hardened, audited environment.
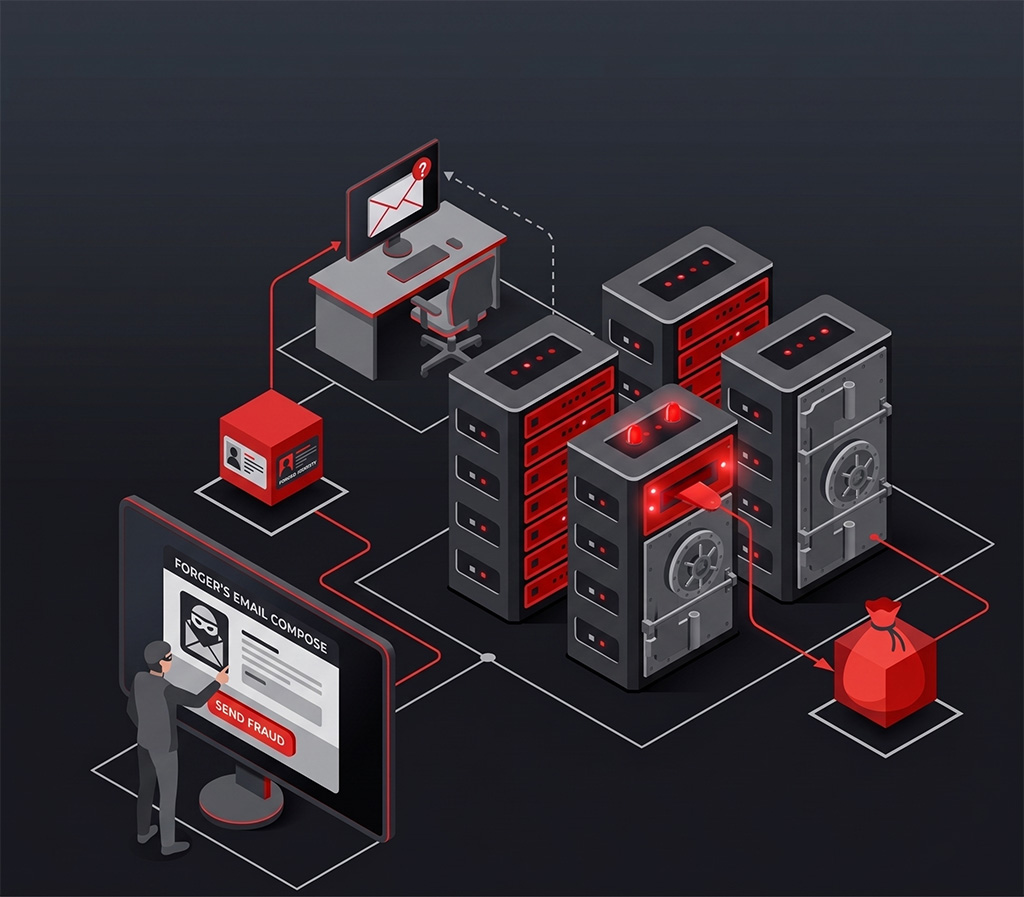
Business Email Compromise (BEC) relies on open SMTP infrastructure and identity replication. SekurMail structurally invalidates the BEC attack vector.
Controlled Intelligence Delivery — SekurSend
Messages do not exist as static copies in external inboxes. Recipients interact with data via a secured, time-bound operational session.
- • Zero Signal Persistence: No message data remains in unvetted external environments.
- • Identity Integrity: Eliminates SMTP-based spoofing and identity replication.
- • Anti-Exfiltration: Structural prevention of unauthorized forwarding or duplication.
Closed-Loop Operational Integrity — SekurReply
All tactical responses occur within the hardened environment, removing the "Reply-Chain" vulnerability.
- • Neutralize Thread Hijacking: Prevents adversaries from inserting malicious payloads into existing conversations.
- • Systemic Isolation: Responses never touch the unsecured public email grid.
Core Technical Parameters
Hardened Encryption Architecture
Multi-layer, end-to-end encryption for data-at-rest and data-in-transit. Keys are generated and managed exclusively within your private environment.
Information Assurance (IA) Protocols
Built for zero-trust models, ensuring data integrity in high-risk operational theaters.
Metadata Signature Suppression
Total elimination of behavioral tracking and signal harvesting. We record zero knowledge of communication patterns.
Jurisdictional Insulation
Hosted on 100% proprietary Swiss hardware, providing a legal and physical shield against foreign discovery.
Sovereign Data Containment
No routing through third-party mail servers, public cloud infrastructure, or external processing layers.
Administrative Lockdown
Centralized policy enforcement with role-based access controls and comprehensive audit capabilities.
Controlled Communications Outside Public Infrastructure
SekurMail operates as a controlled communications environment, isolated from public cloud infrastructure and third-party routing.
- Swiss-hosted infrastructure under exclusive operational control
- No dependency on external mail servers or shared cloud environments
- Administrative control over users, domains, and communication policies, including external recipients
- Configurable data retention API within a contained system
SekurMail
Contained Email System
Controlled Access Configuration
Most organizations do not control where their email travels.SekurMail changes that.Minimum deployment scope applies based on configuration requirements.
Private
Single-user controlled access
No external routing
Controlled recipient access
- Multi-level encryption for emails
- Redundant Storage 150GB
- Up to 5GB file transfer
- 2 factor authentification
- SPF, DKIM keys
- PGP support
- SekurSend protection anti-BEC
- Encrypted Calendar
- Encrypted Tasks
- Time sensitive
- Sekur Monitoring Module
- Alias Up to 20 Free email address
- Unlimited Web and App access
Operational
Team coordination under policy control
Custom domain with defined boundaries
Centralized communication control
- Multi-level encryption for emails
- Redundant Storage 250GB
- Up to 5GB file transfer
- 2 factor authentification
- SPF, DKIM keys
- PGP support
- SekurSend protection anti-BEC
- Encrypted Calendar
- Encrypted Tasks
- Time sensitive
- Sekur Monitoring Module
- Alias (Optional)
- Unlimited Web and App access
- Admin Onboarding
- Mail Archiving
- Custom Domain
Command
Organization-wide communication governance
No external routing across users
Policy enforcement and monitoring
- Multi-level encryption for emails
- Redundant Storage 500GB
- Up to 5GB file transfer
- 2 factor authentification
- SPF, DKIM keys
- PGP support
- SekurSend protection anti-BEC
- Encrypted Calendar
- Encrypted Tasks
- Time sensitive
- Sekur Monitoring Module
- Alias (Optional)
- Unlimited Web and App access
- Admin Onboarding
- Mail Archiving
- Custom Domain
- Sekur Relay C-Level email protection
- Company Directory
- Password policies
High-Volume Deployment & Custom Architecture
For organizations requiring multi-departmental integration, air-gapped configurations, or GSA-schedule procurement. Tailored security posture for defense, government, and regulated industries.
Initiate Strategic ConsultationStrategic Volume Licensing: Tiered pricing for 500+ seat deployments
White-Glove Migration Concierge: Full-spectrum data transition from legacy systems
On-Premise Integration: Deployment within defined organizational perimeters
Dedicated Liaison: Direct access to Sekur technical leadership
The Sovereign Communication Stack
Achieve 100% decoupling from the public grid across all vectors. Structural redundancy ensures your entire signal perimeter is hardened.
Premium Corporate
Core Components
Mail, Messenger, VPN
Infrastructure
500 GB Storage / Password Policy
Support
Migration Concierge
Corporate Plus
Core Components
Mail, Messenger, VPN + Voice/Video
Infrastructure
500 GB / Advanced Admin Controls
Support
Priority Onboarding
On-Premise Deployment
Deploy within your own infrastructure with full administrative control. No external cloud, no third-party routing. Communication remains contained within your operational environment.
Explore deployment optionsEstablish Procurement Channel
Initiate architectural review, obtain deployment specifications, and establish institutional procurement protocols.